From milestone to operational standard
SOC 2 Type II has traditionally been viewed as a milestone—something to achieve and then move past. In today’s security environment, that approach no longer reflects how risk is managed or how trust is built.
❗Threat landscapes change continuously.
❗Vendor ecosystems are more complex.
❗Procurement teams are more rigorous in how they assess third-party risk.
SOC 2 Type II is not a one-time achievement, but is an ongoing operational discipline.
As an organization that maintains SOC 2 Type II compliance, Calian sees how organizations are shifting from certification-focused projects toward sustained compliance models that support long-term security and business resilience.
SOC 2 Type II is designed to measure performance over time
SOC 2 Type II evaluates whether controls are not only designed appropriately, but also operating effectively over a defined period.
Quick comparison: Type I vs. Type II
| SOC 2 Type I | SOC 2 Type II |
|---|---|
| Point-in-time review | Covers controls over time |
| Reviews control design only | Reviews design + effectiveness |
| “Controls exist” | “Controls worked consistently” |
| Lower assurance | Higher assurance (enterprise grade) |
Auditors often describe Type I as a snapshot and Type II as continuous evidence that controls were followed day-to-day. This distinction is critical. It moves compliance beyond documentation and into daily practice.
Organizations that treat SOC 2 as a one-time initiative often experience:
❌ Gaps between policy and execution
❌ Inconsistent evidence collection
❌ Control ownership confusion
❌ Increased operational strain near audit periods
More mature programs embed controls directly into workflows, including:
✔️ Access management
✔️ Change management
✔️ Incident response
✔️ Monitoring and logging
✔️ Secure development practices
In these environments, SOC 2 becomes part of how systems are built and operated—not something layered on after the fact.
Cost of intermittent compliance: Audit fatigue
As buyers place greater emphasis on recertification history and sustained compliance, organizations face a new operational challenge: remaining audit-ready year after year without disrupting core business functions.
For many teams, this pressure surfaces as audit fatigue. It typically results from:
- Manual and repetitive evidence collection
- Fragmented control ownership
- Reactive preparation cycles
- Unclear accountability
The impact is felt most acutely by engineering, IT and security teams, where repeated audit preparation competes directly with product delivery and operational priorities. However, these challenges are rarely caused by SOC 2 itself. They are symptoms of how compliance programs are structured.
Organizations that reduce audit fatigue:
- Centralize control management
- Standardize evidence workflows
- Clarify ownership
- Align compliance activities with operational processes
This is where experienced compliance partners can materially improve outcomes.
Calian’s cyber solutions team supports this shift by structuring control programs, validating readiness, and managing auditor interactions—allowing internal teams to focus on business priorities rather than audit logistics.
Sustainable compliance is not about working harder at audit time.
It is about building systems that make audits routine.
What continuous compliance looks like in practice
Continuous compliance does not require constant audits. It requires controls that:
- Operate consistently throughout the year
- Are monitored regularly
- Are supported by current documentation
- Have clear accountability
In these environments, organizations shift from asking:
“Are we ready for the audit?” to “Are our controls working today?”
This shift enables:
- Faster response to customer security assessments
- Lower audit risk
- Reduced operational disruption
- Stronger confidence with customers and partners
SOC 2 becomes a mechanism for maintaining trust, not just demonstrating it.
Practical SOC 2 Type II journey
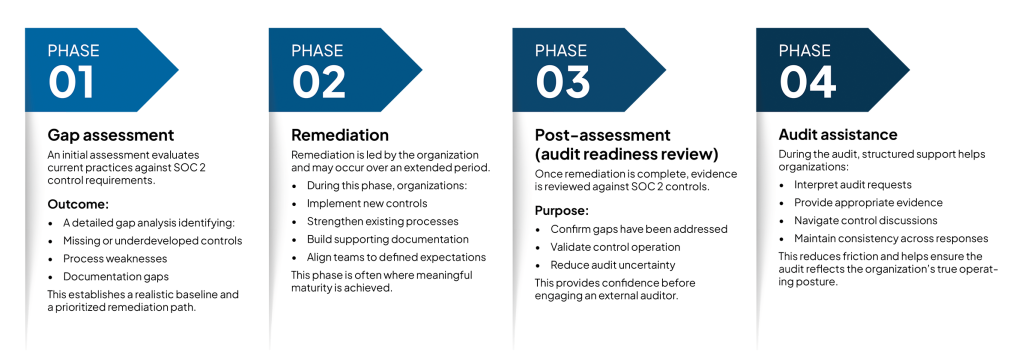
Organizations pursuing SOC 2 Type II typically progress through four structured phases.
From certification to confidence
SOC 2 Type II was designed to assess whether organizations can operate securely and consistently.
Organizations that approach SOC 2 as a living system rather than a static milestone gain:
- Stronger customer trust
- Shorter procurement cycles
- Reduced operational risk
- More sustainable security programs
As an organization that maintains SOC 2 Type II compliance through recurring audits, Calian views continuous compliance as an operational standard aligned with how modern organizations must manage risk.
SOC 2 Type II is no longer the destination. It is the baseline.
calian.com/digital-cyber | 24/7 Incident reporting hotline: 1.833.485.3760
